En/4.1/OpenChange (Microsoft(R) Exchange Server protocol implementation)
Introduction to OpenChange Technology
Zentyal integrates OpenChange, the first and only native implementation of Microsoft® Exchange Server protocols in Linux. With OpenChange, Microsoft Outlook® clients continue to work unchanged, without needing any plug-ins, reconfiguration or migration.
OpenChange achieves complete compatibility because it implements the same MAPI (1) protocols as existing mail and groupware clients: the MAPI protocol, and optionally ActiveSync®. These protocols manage, not just the electronic mail, but also contact lists and calendars.
In addition to being a MAPI server, OpenChange is a bridge between MAPI and these Internet-standard protocols (IMAP, SMTP, CalDAV, etc), keeping both sides synchronized. A message in the Microsoft Outlook® inbox is visible in Mozilla™ Thunderbird's view of the same account via IMAP, and when deleted the message disappears from both sides. Similarly, a calendar entry made in Mozilla™ Lightning over the CalDAV protocol is visible and modifiable from Microsoft Outlook®.
OpenChange itself is a Samba4 plug-in, using Samba4 to retrieve user information, perform authentication and access the Global Address List directory service, which contains the user accounts belonging to the organization.
As previously mentioned, the Microsoft Outlook® client can communicate natively with this component, there is no need to re-join the client to a domain or to install any external software.
Apart from the connections established within the organization's network, your Microsoft Outlook® clients can connect from any point of the Internet thanks to the MAPI Proxy (Outlook® Anywhere) component, able to encapsulate the protocol using HTTP/RPC.
Zentyal offers a Webmail platform integrated with OpenChange. Using this platform, you can offer a HTTP/HTTPS gateway to interact with all the mentioned mail and groupware features.
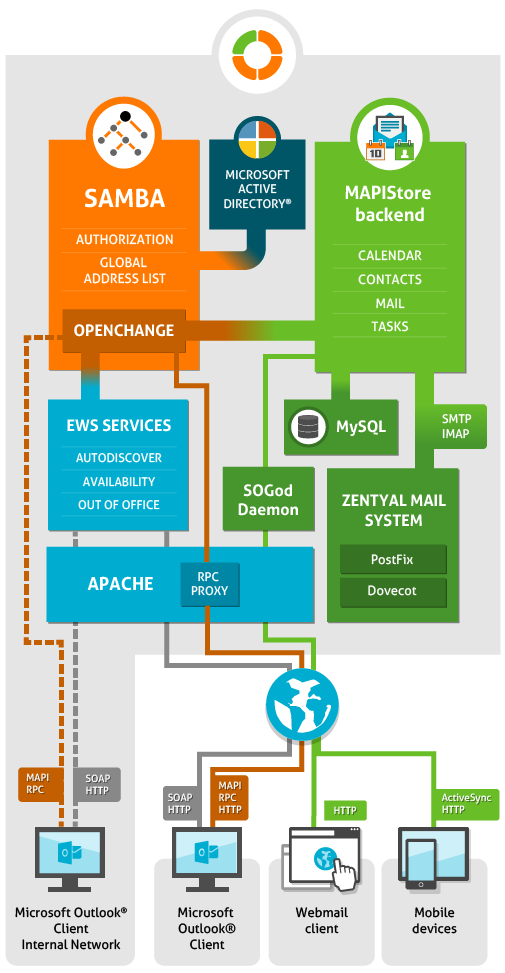
Architecture Overview
To get an overview of where is OpenChange located in relation to the other Zentyal Components and the basics of its interactions and protocols you can review the next diagram:
At the bottom of the diagram there are shown a different range of connections which can access our mail and groupware infrastructure. Starting from Microsoft Outlook® clients from internal or external networks, and finishing with connections from the webmail interface and mobile devices.
Microsoft Outlook® clients located in the internal networks are typically configured to use MAPI protocol; while those connecting to an external network should make use of Microsoft® Outlook Anywhere technology.
The infrastructure deployed to process those connections can be better understood thinking of the whole system as a layered one. First layer would be placed at Apache and HA Proxy level. In that layer connections will be delivered to the appropriated component of the layer underneath, they serve as the frontal proxies. At that second layer you can find OpenChange and Samba. They will accept connections to provide data and grant a proper authentication. The third layer handles the data. In this case mails, events, contacts and tasks are stored and managed in MySQL database and IMAP folders. To handle with SMTP and IMAP protocols (sending and storing mail messages) you can also find Postfix and Dovecot.
Internal MAPI query (dashed orange and dashed gray)
In this case the client can communicate natively with OpenChange using the MAPI/RPC protocol. OpenChange will be in charge of querying the other components to reply.
Microsoft® Outlook Anywhere (solid orange and solid gray)
The previously commented MAPI/RPC protocol is encapsulated inside a HTTP(S) session, thus it will arrive to the first layer where, at the end, Apache, using the RPCproxy WSGI, will unencapsulate the protocol and perform the MAPI calls to the OpenChange component.
Browser access and mobile ActiveSync® (green)
Webmail requests are pure HTTP performed by the web client, while ActiveSync® is based on XML inside HTTP. Thus, in both cases, the first layer will end up with Apache using a 'proxy_pass' to the 'sogod' daemon.
EWS Services (accessed by dashed and solid gray)
These requests use SOAP/XML over HTTP. As shown at the diagram they can be performed from both internal and external clients. Those requests will reach the first layer, which will be in charge of routing them to the OCSManager. The OCSManager will perform the appropriated queries to return the Autodiscover information and EWS operations after querying both Samba and OpenChange.
Configuring the OpenChange server in Zentyal
There are some steps you have to address before running the OpenChange provision. If you go to Mail‣OpenChange some information boxes will be shown with the necessary steps to follow to be able to perform the initial configuration. The installer wizard will perform most of these steps for you if you have included the Mail and Groupware module.
- Enable the OpenChange module at Module Status.
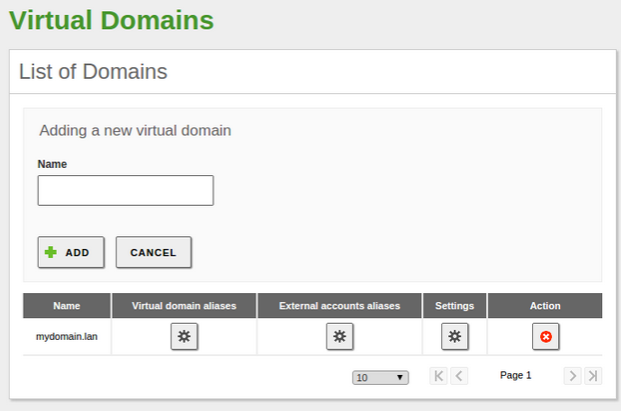
- You have to create a virtual mail domain. Go to Mail ‣ Virtual Mail Domains and create one. That domain
will be used to provision Samba and OpenChange.
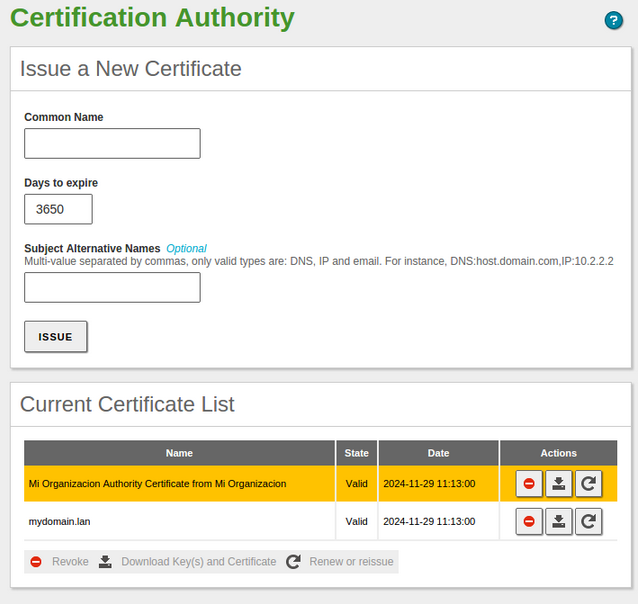
- You also need a CA certificate. So go to CA ‣ General and create one. Do not forget to fill all the form fields.
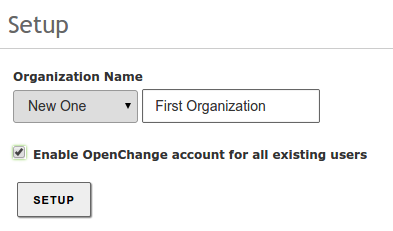
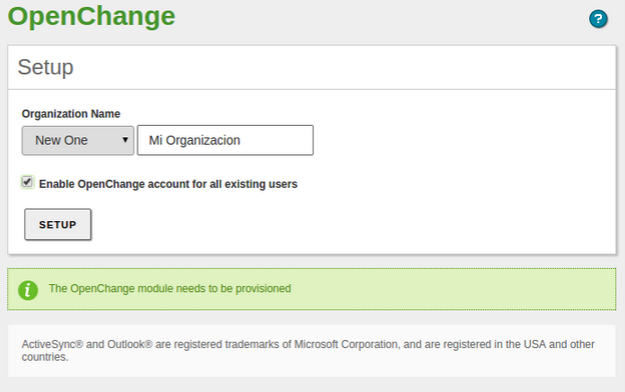
Once you have checked all the previous points, you can choose your Organization Name. You have a checkbox available in case you want
to provide an OpenChange account for all the existing users in your directory. Once you click on Setup, a Save Changes process will
be launched
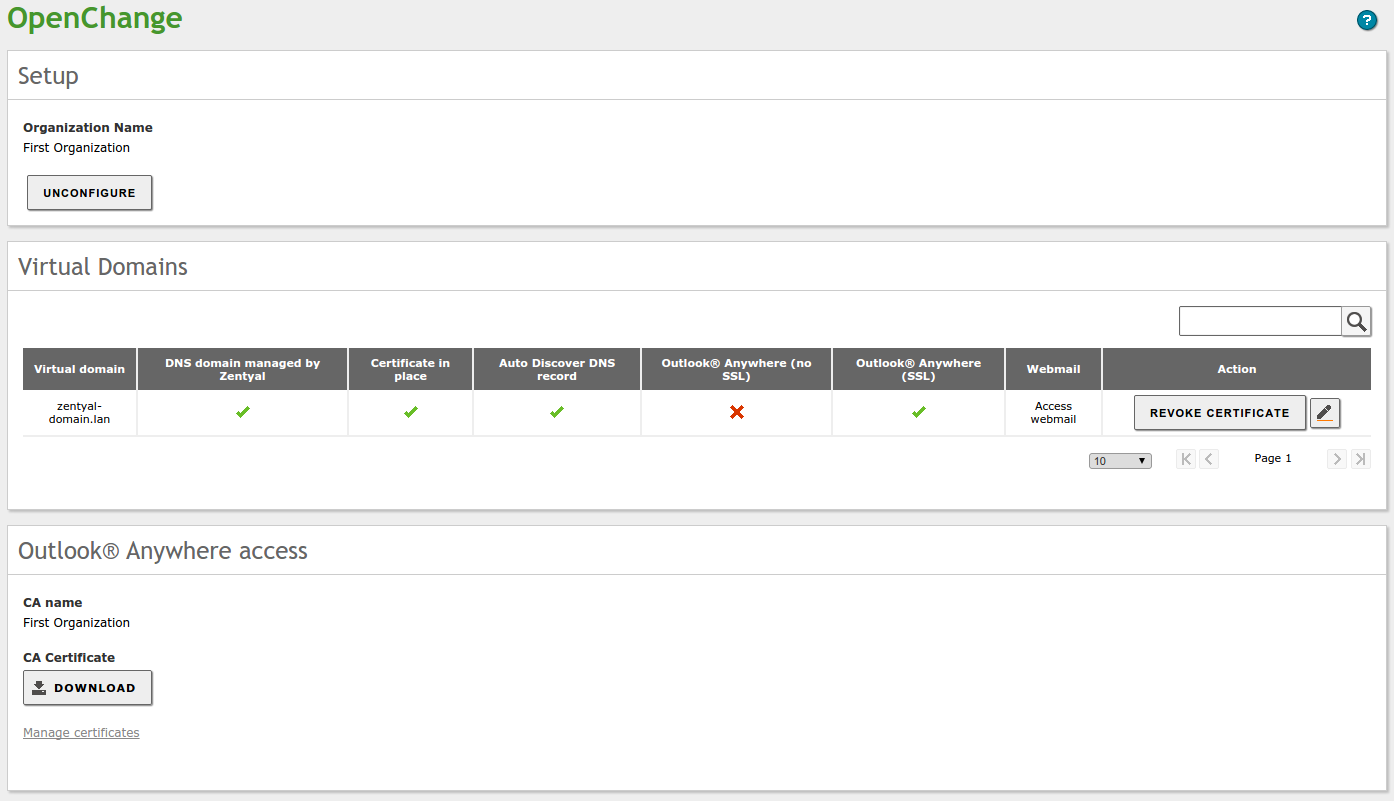
Once you complete the setup (or if everything has been auto-configured by the installation wizards), you will see the following interface:
This general OpenChange configuration interface could take a few seconds to load, it needs to query several other Zentyal components to provide all the information for the virtual mail domains capabilities.
On the top, there is a block where you can see your organization's name and you can Unconfigure, destroy all directory information and user accounts related with OpenChange. You should need this option only if you want to change the Organization Name.
The middle block is the most complex one, here you can see the detailed status for each one of the virtual mail domains that you configured from Mail ‣ Virtual Mail Domains.
DNS domain managed by Zentyal
Whether or not Zentyal's DNS module is acting as the authoritative server for this domain. If you are configuring your domain in an external DNS you may not need this. Both yourdomain.name and autodiscover.yourdomain.name need to be resolved by the client. If this check is green, it means that Zentyal is already resolving these names.
Certificate in place
Microsoft Outlook® clients are going to require a certificate that matches the common names of the hosts specified in the DNS. Using the Issue Certificate button, you can automatically create the appropriate certificates for this domain. If the check is green, you already have the certificate in place, and can revoke it with the button.
Autodiscover DNS record
Whether or not the autodiscover.yourdomain.name (as mentioned before) is present in Zentyal's DNS, this hostname and its associated certificate is needed to autoconfigure the Microsoft Outlook® clients.
Outlook Anywhere® (no SSL)
The MAPI/RPC gateway that was detailed in the architecture overview, needed to process Outlook Anywhere® traffic. Non-SSL version.
Outlook Anywhere® (SSL)
The MAPI/RPC gateway that was detailed in the architecture overview, needed to process Outlook Anywhere® traffic. SSL version.
Webmail
You will have a link to access the webmail application. It will have the format http(s)://<your_IP_or_domain>/webmail.
For the example above:
- zentyal-domain.lan is managed by Zentyal.
- autodiscover.zentyal-domain.lan is present in the DNS as well.
- I have a proper certificate for both names.
- I can access my account using Outlook Anywhere®, only if I use SSL.
- I can access my webmail using the URL: https://zentyal-domain.lan/webmail.
By clicking on the Edit button at the right, you can enable or disable any of these capabilities for the virtual mail domain.
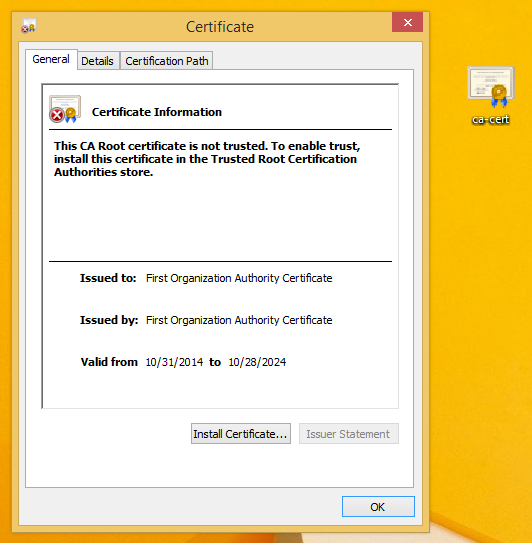
Finally, at the bottom block you can check your current Certification Authority name and download the CA certificate. Take into account that in order to trust any Zentyal secure service, including the mail services, the client needs to trust the associated CA first. This is specially important for Outlook Anywhere®.
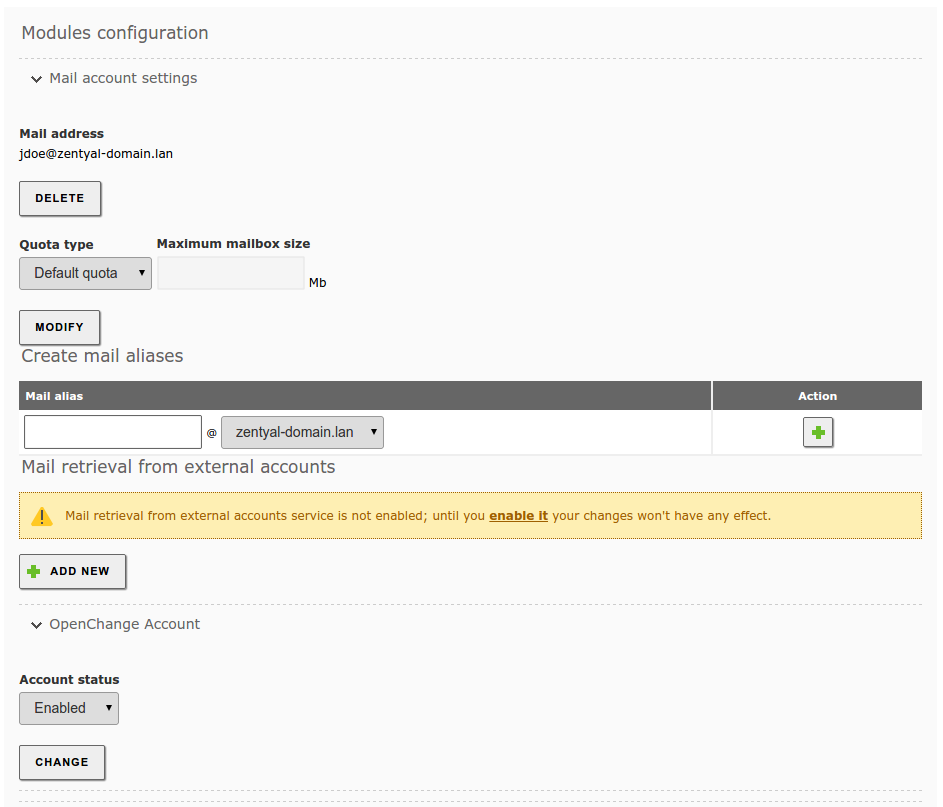
To access the mail account using Microsoft Outlook®, a user needs to have the OpenChange capabilities enabled for his/her account, you can check that accessing Users and Computers ‣ Manage, clicking on the user and displaying the mail plugins at the bottom-right.
You can always configure whether the new users will have OpenChange enabled by default from the user template, Users and Computers ‣ User Template.
Configuring the Microsoft Outlook® Client
There are basically three different configuration scenarios:
- The client is inside the organization's network and joined to the domain
- The client is inside the organization's network but not joined to the domain
- The client wants to use Microsoft Outlook® from an external network (Outlook® Anywhere)
Enabling the autodiscover service will greatly ease the process for the user, since all the server parameters will be configured automatically.
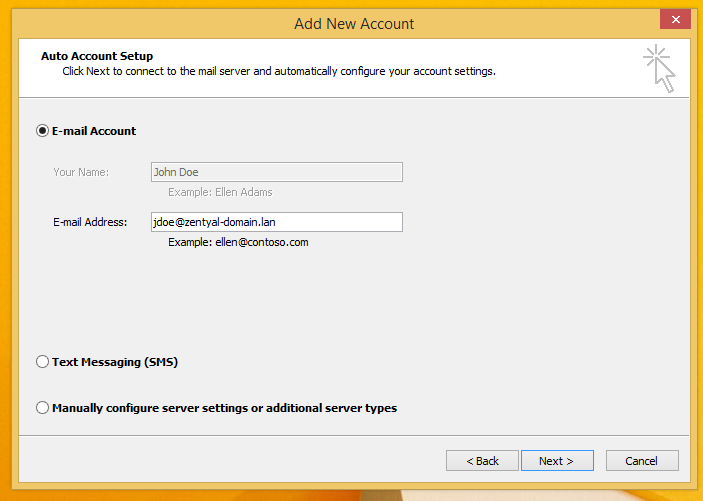
The first case is fairly straightforward, because the user's credentials are already loaded at login. Assuming that you have logged in with the same domain user that you want to use for email, you just need to click through the wizard.
Credentials are auto-detected.
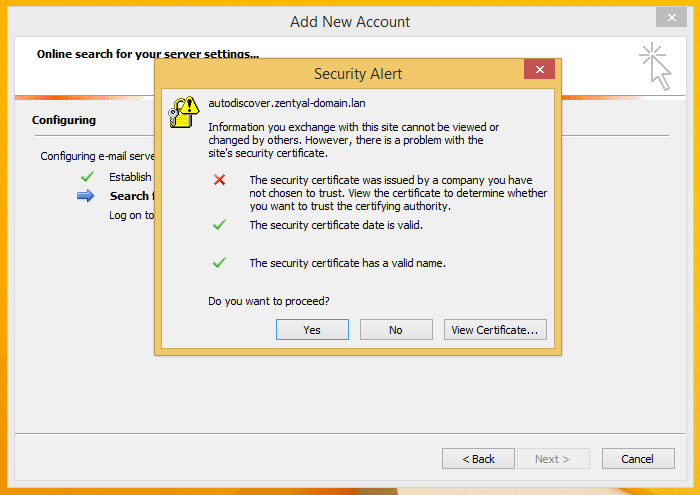
You may have a service certificate warning in case you have not imported Zentyal's CA in the client, it is safe to proceed.
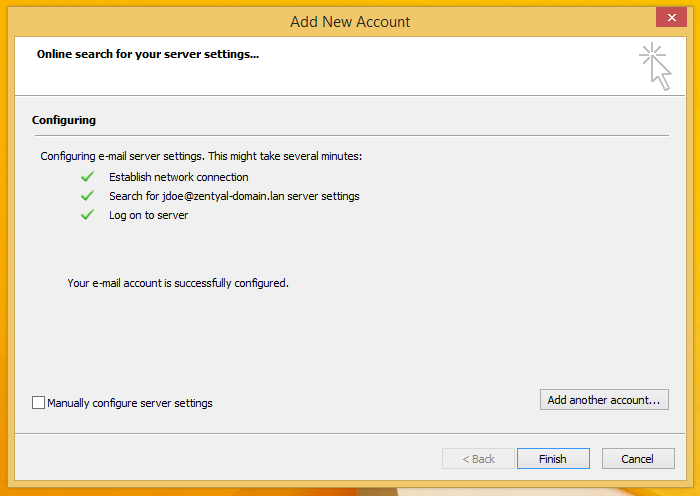
Server settings are autodetected, your mail client is ready to be used.
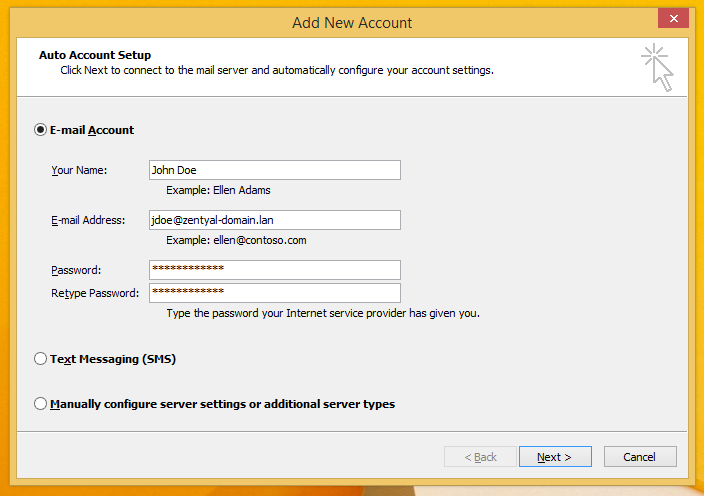
If you are inside the organization, but not joined to the domain, the only difference is that you will need to provide user credentials.
If you want to use Outlook® Anywhere, typically when your accessing from an external network, it is required to import Zentyal's CA certificate.
Store the CA cert in the client, you can use the OpenChange interface to download it.
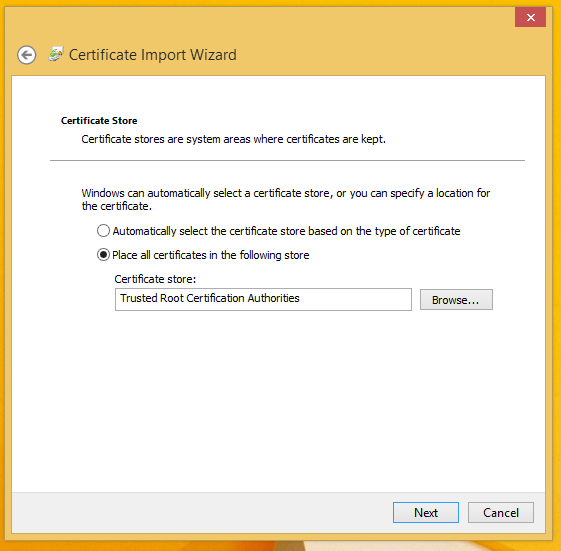
Click on Install Certificate and place it on the Trusted Root Certification Authorities storage.
After you import the CA certificate, you should be able to create your account normally if the autodiscover service is enabled for your virtual mail domain and Zentyal firewall is allowing connection to ports 443 and 80. Remember that the client should be able to resolve both yourdomain.name and autodiscover.yourdomain.name to the correct IP address.
Export/Import Microsoft Outlook® accounts
If you with to move the mail account to a Zentyal Server, you can do it using PST files (2).
Although it is possible to migrate email, calendars and contacts using a PST file, it is recommended to move first just the email between the server using a tool like IMAPCopy and later on import the calendars and contacts using a PST file.
Configuring 'Out Of Office' notifications from the Microsoft Outlook® client
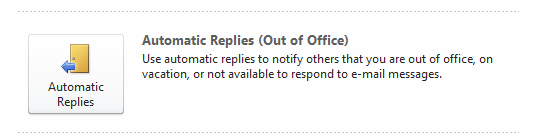
One of the most common mail filters that your users may want to configure is the automatic response in case of not being available at the office for an extended period, so their partners will be aware that their messages will not be replied in the short term.
From your Microsoft Outlook® client, you can use the assistant to configure Out Of Office
Where you will be able to configure the following options
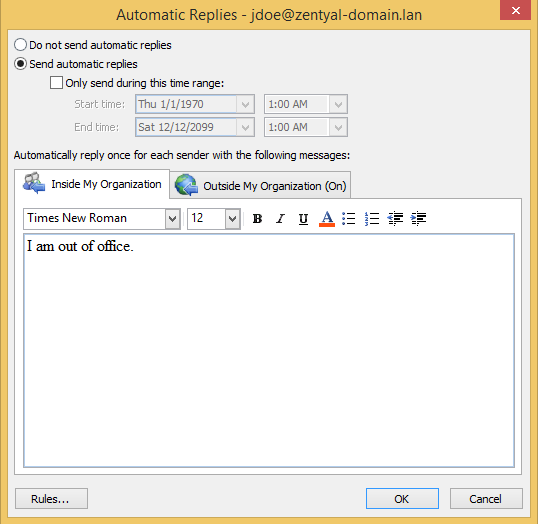
From this interface, you can configure the time period and the desired message to be replied. It is important to check the current limitations present in this feature, described at the end of this document.
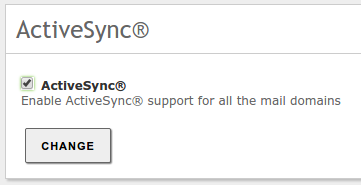
ActiveSync® support
The ActiveSync® protocol is widely used to synchronize mobile devices.
There is a software package which provide this functionality on top of OpenChange (sogo-ActiveSync®), it is recommended to install it through the command line with:
sudo apt-get install sogo-activesync
Once you have installed, you will be able to enable or disable the ActiveSync® option from the OpenChange interface.
Different devices support a different set of ActiveSync® features (3)
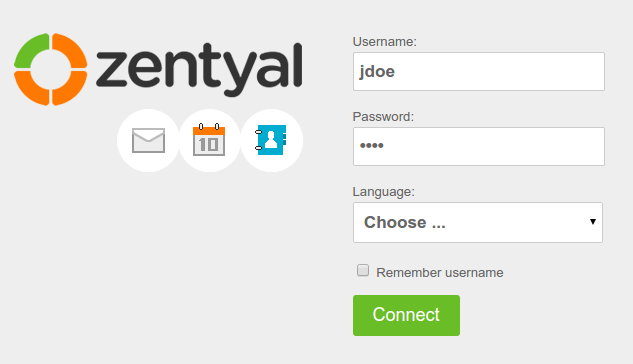
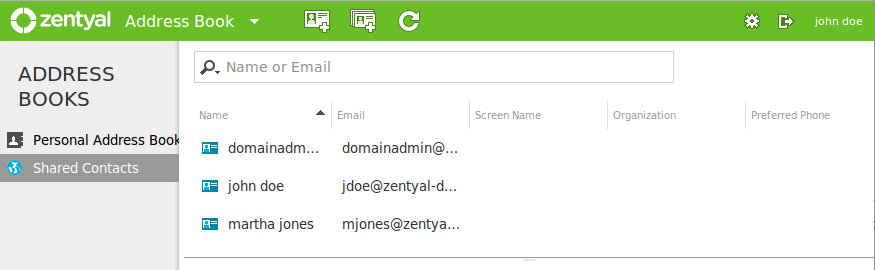
OpenChange Webmail
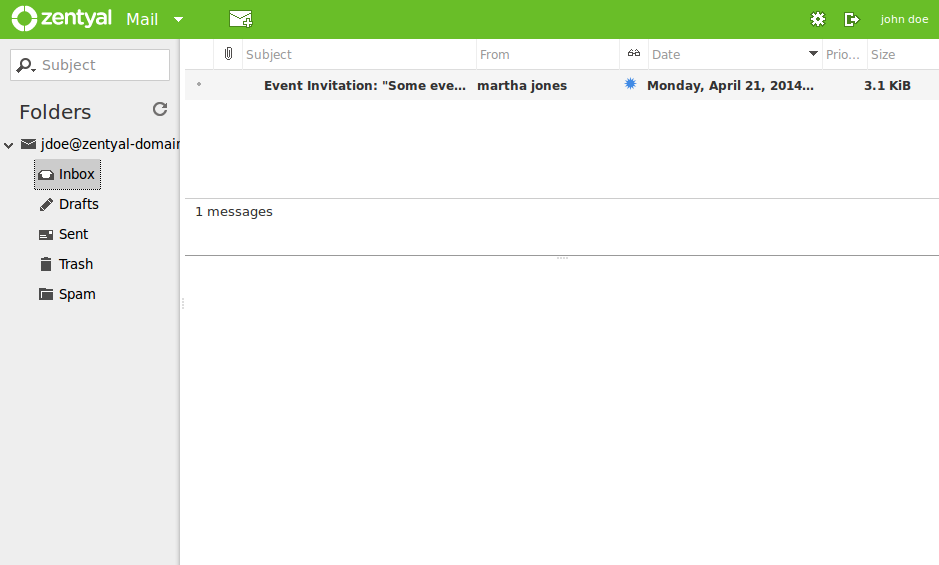
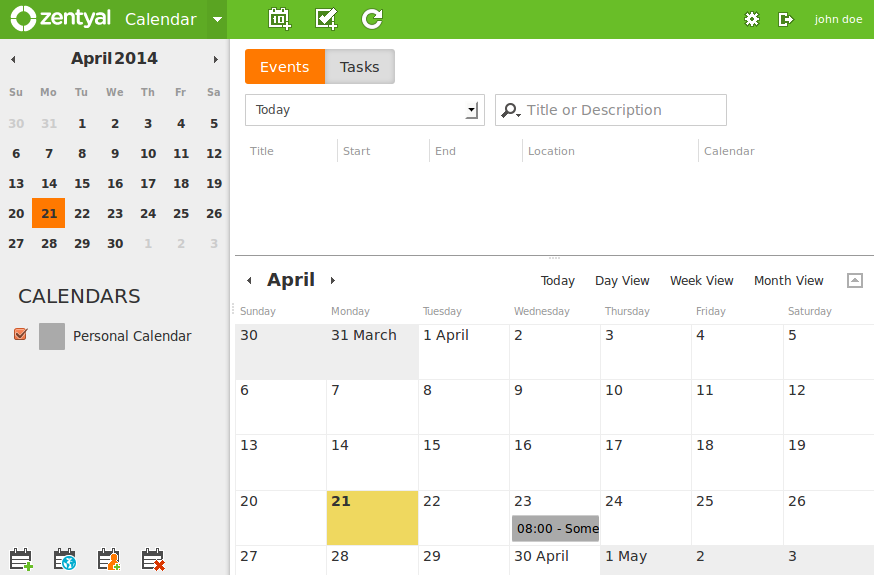
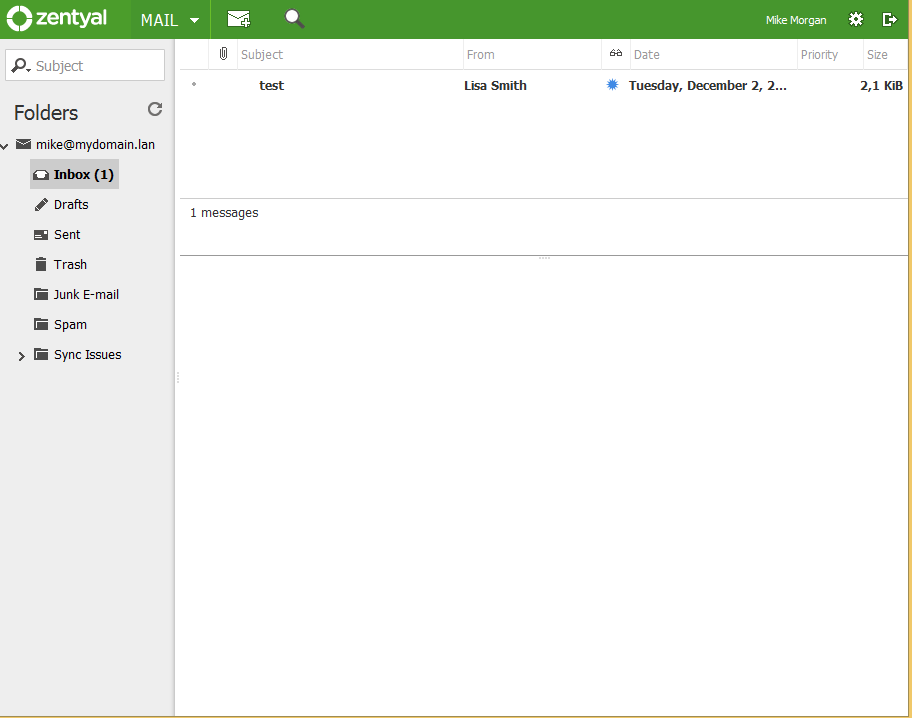
Apart from the described functionality using native clients, it could be very useful to deploy a web based client to access our e-mail, calendars and contacts. This way, our users can access their mail and groupware data from anywhere using just a web browser.
Once you have enabled the capability, you can access the web platform accessing the URL http(s)://<server_IP_orFQDN>/webmail/
You will first be shown the email interface
Using the drop down menu that you have available in the top part of the interface, you can access the calendars:
And also the address book, where you can view the Global Address List (GAL), which contains all the users registered in your domain, the personal address books of the user and custom distribution lists that can be used for mailing,
Known Limitations
It is important to note that the set of features provided by the Microsoft Outlook® client is large, in this document we are considering the typical set of features that the average user will require to complete his/her daily tasks.
The following features are not available on the common Microsoft Outlook® versions (2003, 2007, 2010):
- Only the users inside the OU 'Users' can have OpenChange mail accounts
- Sending a mail with an embedded mail attached
- Using special characters in the mail address (like áéíóúñÑ)
- Sending a contact via mail using Microsoft Outlook® format (vCard format is working)
- Assigning a task to a contact
- The 'Out of Office' functionality is only available for Microsoft Outlook® 2007 and 2010
- If the 'Out of Office' notification is enabled, only the date is applied, time is ignored
- You cannot set different 'Out of Office' messages, just one for all the recipients
- You cannot use the characters '.' or '/' for the names of mail directories
- You cannot use empty spaces ' ' for Active Directory usernames, it will not function with OpenChange
- No automatic mail refresh, user needs to manually Send/Receive or configure a polling mechanism
- No public folders support
- Outlook for MacOS systems is not supported
- Tasks created in Outlook are local to Outlook (not synced with Webmail and other protocols)
- Rules created in Outlook clients doesn't get synched to the server (Use the server side filters setting them in webmail)
Practical examples
Practical example A
In this example we are going to configure an OpenChange account from scratch, using a Zentyal server with OpenChange already installed (dependant modules will be installed automatically) and all required modules activated. First we will need a to add a virtual mail domain.
Then we perform an initial OpenChange setup for all users of the domain.
We will also need a Certification authority. The OpenChange module will also facilitate this process with a button to issue the certificate.
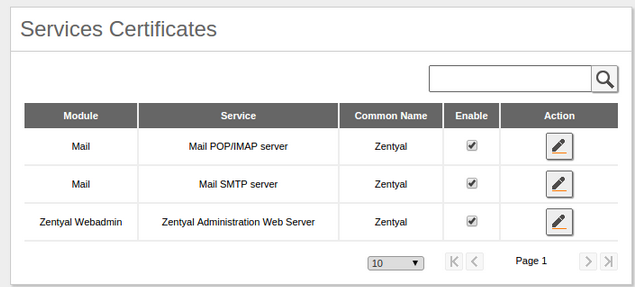
Finally we have to enable the certificates for the mail services to finish up the OpenChange configuration in our server.
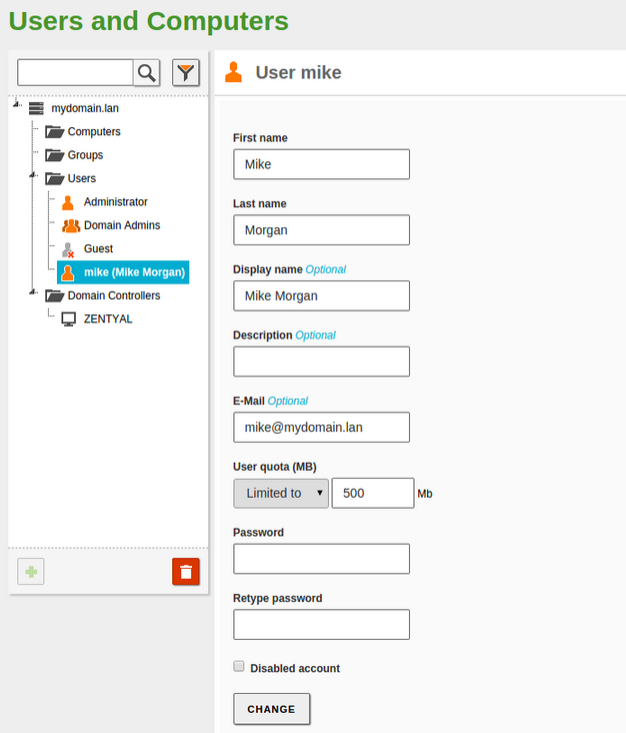
OpenChange is ready, we check that is working properly from a Windows® client. We will need a user so we go to 'Users and Computers-->Manage' to create it.
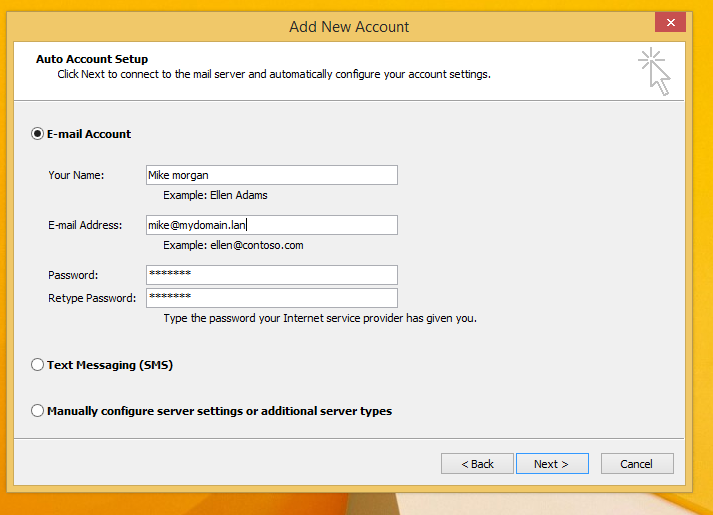
We set up the Outlook® account in the Windows® client. We have to make sure there is nothing blocking the client in the LAN, the firewall module opens the required ports by default. After introducing the data of the account our user and domain will be detected by the wizard as shown below.
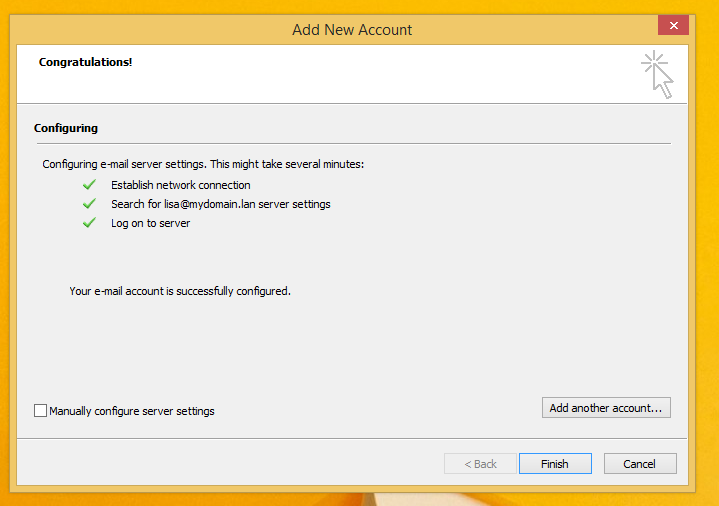
If the account is well set up, we will see the following screen.
We proceed after the security alert.
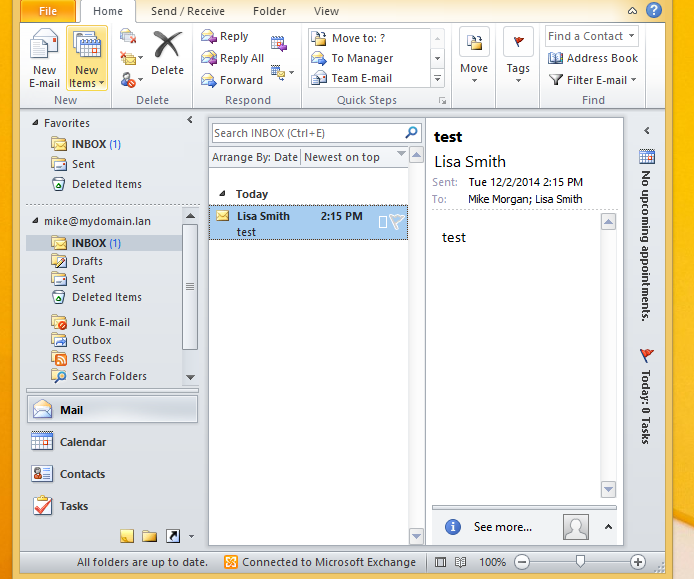
Finally we make a test to see that communications are working.
Practical example B
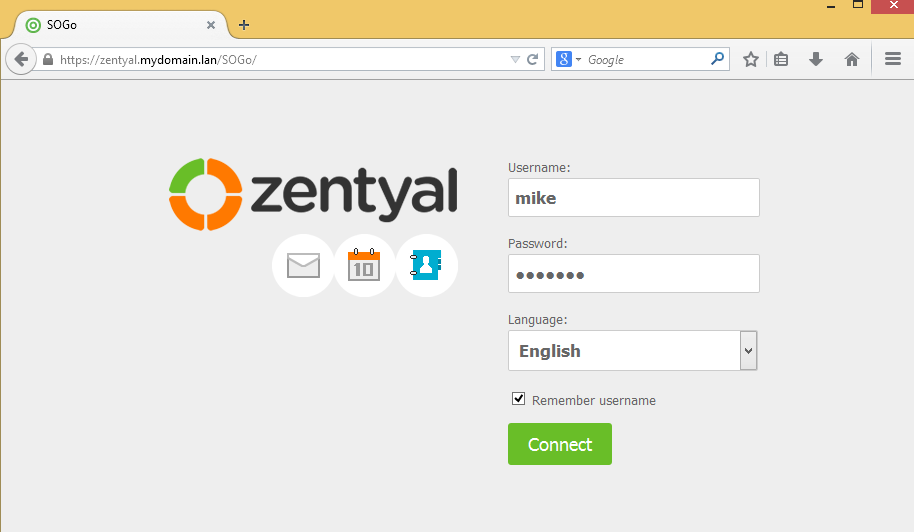
In this example we are going to use the webmail service in Zentyal. Ports should be open by default in the firewall when modules are installed and activated. We can access webmail at: http(s)://<IP_or_FQDN>/webmail/
We can check that everything is correct with the account set up in practical A.