En/2.2/High-level Zentyal abstractions
Contents |
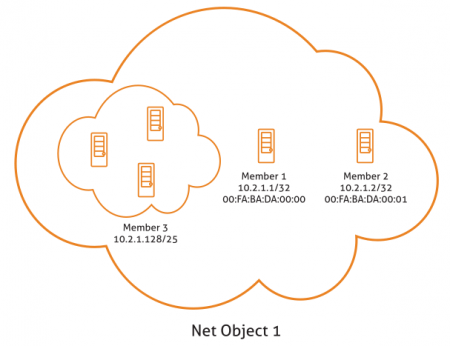
Network objects
The Network objects are a way to represent network elements, or a group of them. They allow you to simplify and consequently make it easier to manage network configuration: network objects allow you to give an easily recognisable name to elements or a group of them. This means you can apply the same configuration to all elements.
For example, you can give a recognisable name to an IP address or a group of them. Instead of defining the same firewall rule for all IP addresses, it is enough to define it for the network object that already contains the addresses.
Management of Network objects with Zentyal
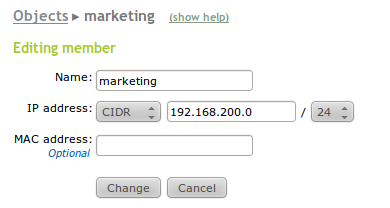
To start to work with the Zentyal objects, go to Network ‣ Objects section. Initially you will see an empty list; with the name of all the objects and a series of actions you can carry out on each of them. You can create, edit and delete objects that will be used later by other modules.
Each one of these objects consists of a series of members that can be modified at any time. The members must have at least the following values: Name, IP Address and Netmask. The MAC address is optional and logically you can only use it on members that represent a single host. This value will be applied when the MAC address is accessible.
The members of one object can overlap with members of other objects. Therefore you must be careful when using them in the other modules to avoid conflicts.
In other configuration sections of Zentyal where you can use network objects ( like DHCP or Firewall), a quick embedded menu will be offered, so you can create and configure the network objects without explicitly accessing this menu section.
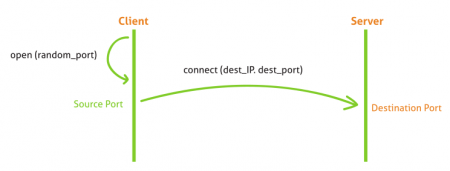
Network services
Network services is a way to represent the protocols (TCP, UDP, ICMP, etc) and the ports used by applications. The purpose of the services is similar to that of the objects: objects simplify reference to a group of IP addresses with a recognisable name. Services allow identification of a group of ports by the name of the services the ports have been allocated to.
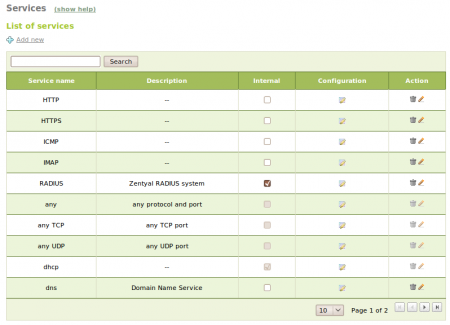
When browsing, for example, the most usual port is the HTTP port 80/TCP. But in addition, you also have to use the HTTPS port 443/TCP and the alternative port 8080/TCP. Again, it is not necessary to apply a rule that affects the browsing of each one of the ports, but the service that represents browsing and contains these three ports. Another example is the file sharing in Windows networks, where the server listens to the ports 137/TCP, 138/TCP, 139/TCP and 445/TCP.
Management of Network services with Zentyal
To manage services with Zentyal, go to Network ‣ Services menu, where you will find a list of available services, created by all the installed modules and those that were added later. You can see the Name, Description and access the Configuration. Furthermore, each service has a series of members; each one contains Protocol, Source port and Destination port values. You can introduce the value Any in all of the fields to specify, for example, the services for which the source port is different to the destination port.
TCP, UDP, ESP, GRE or ICMP protocols are supported. You can also use a TCP/UDP value to avoid having to add the same port twice when both protocols are used by a service, for example DNS.