En/2.2/File sharing and authentication service
Contents |
Introduction to files sharing and authentication
Zentyal uses Samba (4) to implement SMB/CIFS.
Configuring a file server with Zentyal
The file-sharing services are active when the file sharing module is active, even if the PDC is not.
File sharing is integrated with users and groups. Each user has a personal directory and each group can be assigned a shared directory.
The user's personal directory is automatically shared and can only be accessed by the user.
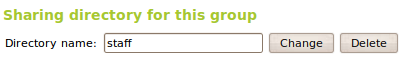
It is also possible to create a shared directory for a group using Users and Groups ‣ Groups ‣ Edit group. All group members have access to that directory and can read or write to all the files and directories within the shared directory.
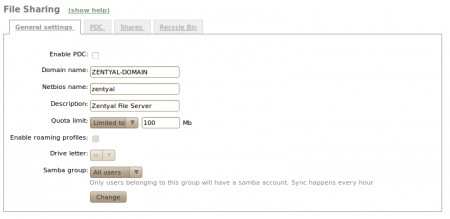
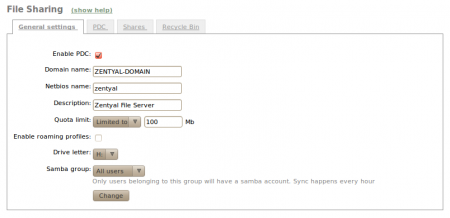
To configure the general settings of the file sharing service, go to File Sharing ‣ General configuration.
The domain is set to work within the Windows local network, and the NetBIOS name is used to identify the Zentyal server. You can use a long description to describe the domain. In addition, there is the option to set a quota limit. Using Samba Group it is possible to configure an exclusive group where member users are assigned an account for file sharing.
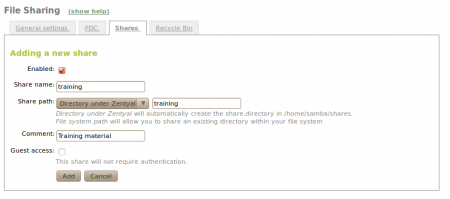
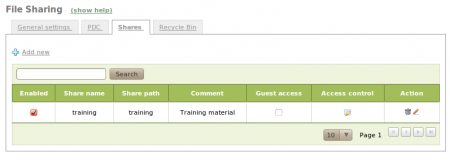
To create a shared directory, use File Sharing ‣ Shares and click Add new.
Enabled:Leave it checked if this directory needs to be shared. Disable to stop sharing.
Share name:The name of the shared directory.
Share path:Directory path to be shared. You can create a sub-directory within the Zentyal specific directory /home/samba/shares, or use an existing file system pathway by selecting Filesystem path.
Comment:A more detailed description of the shared directory simplifies management of shared assets.
Guest access:Enabling this option allows a shared directory to be accessible without authentication. Any other access settings will be ignored.
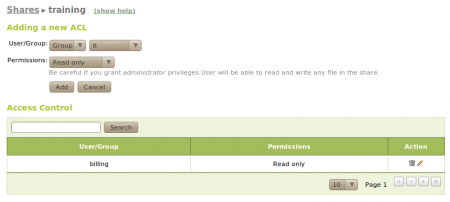
Shared directories can be edited using Access control. By clicking on Add new, you can assign read, read/write or administration permissions to a user or group. If a user is a shared directory administrator, he/she can read, write and delete any user files within that directory.
You can also create a share for a group using Users and Groups ‣ Groups. All group members will have access: they can write their own files and read all the files in the directory.
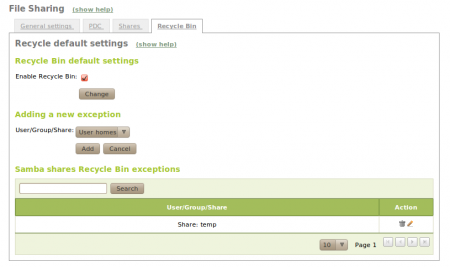
If you want to store deleted files in a special directory called RecycleBin, you can check the Enable recycle bin box using File Sharing ‣ Recycle bin. If you do not want to use this for all shared resources, add exceptions using Resources excluded from Recycle Bin. Other default settings for this feature, such as the directory name, can be modified using the file /etc/zentyal/samba.conf.
Using File Sharing ‣ Antivirus virus scanning of shared resources can be enabled and disabled. Exceptions can also be defined where virus scanning is not required. To use this feature the package samba-vscan must be installed on the system. Also, the Zentyal antivirus module must be installed and enabled.
Samba client configuration
Configuring a Zentyal authentication server
To harness the potential of the PDC as authentication server, and its Samba implementation for Linux, check the Enable PDC box using File Sharing ‣ General Configuration.
If the Roaming Profiles option is enabled, the PDC will not only authenticate users, but will also store their profiles. These profiles contain all the user information, including preferences in Windows, Outlook email accounts and documents. When a user logs in, the user profile will be retrieved from the PDC server. Therefore, the user will have access to their work environment on multiple computers. Before enabling this option, you must consider that the user information can be several gigabytes in size, therefore the PDC server must contain enough disk space. You can also configure the drive letter to which the personal user directory will be linked after authenticating against the PDC in Windows.
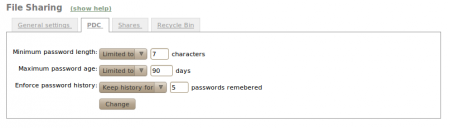
You can set password policies for users through File Sharing ‣ PDC.
- Minimum password length.
- Maximum password age, the password must be renewed after the
the set days have passed.
- Enforce password history, this option will force the recording
of password history, making it impossible for the user to use repeated passwords.
These policies are applicable only when you change the
Windows password from a machine that is connected to your
domain. In fact, Windows will force compliance with this policy
as a machine is registered on the domain.